Top 15th in the nation
The future of pharmacy starts here.

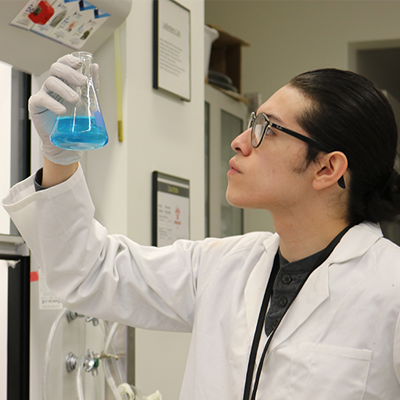
At the Skaggs School of Pharmacy, students from around the globe learn from award-winning faculty in a world-class medical setting. Hands-on training is dynamic, interprofessional and career-driven. From on-campus and remote PharmD pathways to PhD and Master’s degrees, our curriculum is innovative and agile, preparing students to be leaders in the emerging pharmacy careers of the future.
Explore Our Programs

PharmD Program
Interprofessional, experiential, and now with a remote pathway. From hospitals and industry settings, to clinics and pharmacies, our PharmD graduates are taking the lead optimizing medications and improving patient care.
Masters in Pharmaceutical Sciences
The multidisciplinary field of pharmaceutical sciences has seen rapid advances that are critical to the discovery and development of drugs for chronic diseases such as cancer and diabetes, and emerging threats such as new pathogens and drug resistance.

Cannabis Science and Medicine
Online, interactive and evidence-based offerings for healthcare professionals and researchers who want to improve patient care and cannabis science.
 See How CU Pharmacy is Embracing Change and Innovation
See How CU Pharmacy is Embracing Change and Innovation
Pharmacy Perspectives is the official magazine of the CU Skaggs School of Pharmacy and Pharmaceutical Sciences, showcasing the groundbreaking work, inspiring stories, and academic excellence of our faculty, students, alumni, and partners. This issue highlights the impactful research, innovative education, and community engagement that define our school.
Read Now
Top 10% in NIH funding
91% of grads employed within 1 year
1/3 of curriculum is experiential
More than 1,900 rotation sites
Award-winning faculty
Explore Our Campus
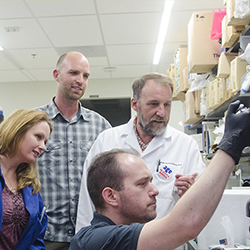
Learn on an Interprofessional Team
From the first week on campus, you’ll engage in experiential and interprofessional training that prepares you for team-based pharmacy careers.
Upcoming Events
Loading items....
Loading items....